Definition
Advanced Encryption Standard
The Advanced Encryption Standard (AES) is a symmetric block cipher and a variation of the Rijndael algorithm developed by Joan Daemen and Vincent Rijmen, and was standardised in 2001.
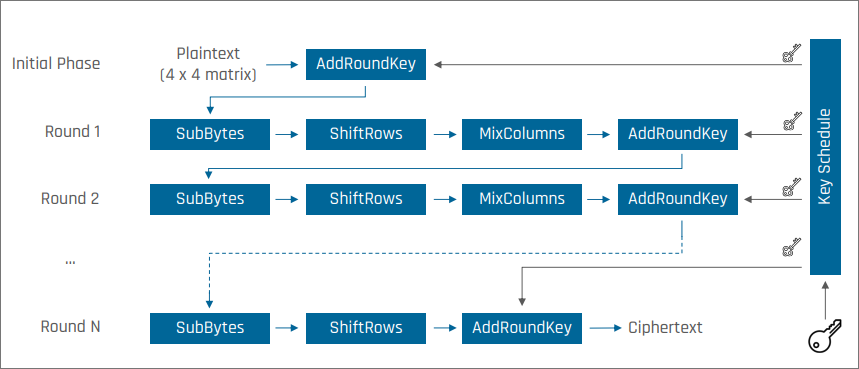
AES has a fixed block size of 128 bits and a variable key size:
Key size (bits) Rounds 128 10 192 12 256 14
Transformations
Each round applies four transformations:
- SubBytes
- ShiftRows
- MixColumns
- AddRoundKey
The final round omits MixColumns.
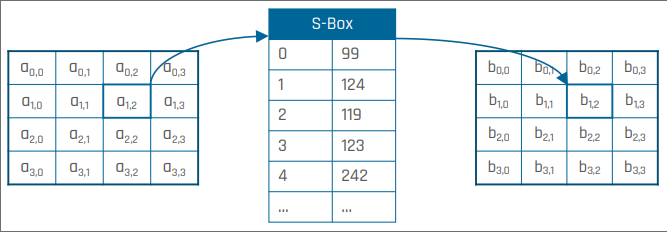
SubBytes
Every byte in the current state is substituted with another byte according to a fixed substitution table (S-Box).
Why?
This transformation introduces non-linearity in the cipher and provides resistance against differential and linear cryptanalysis.
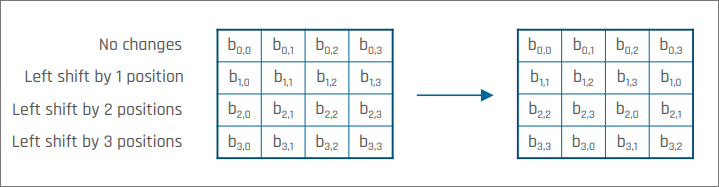
ShiftRows
State elements are left-shifted by an offset that depends on the line.
Why?
Each column of the output state contains an element from each column of the initial one. This prevents columns from being encrypted separately, ensuring that bytes from different columns interact.
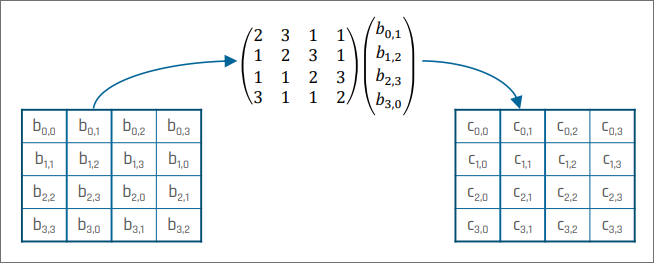
MixColumns
Each column of the state is multiplied with a fixed matrix.
Why?
Each input byte affects all output bytes of the column. This contributes to diffusion (together with ShiftRows).
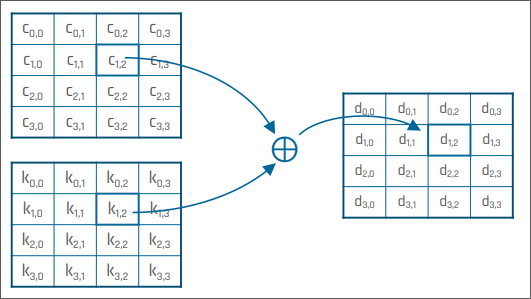
AddRoundKey
The subkey for the current round is XORed with the current state.
Why?
Subkeys are derived from the original key using XOR, cyclic shifts, and substitutions. This step ensures the key material is mixed into the state in every round.
Mode of Operation
AES operates on fixed-size blocks. To encrypt longer messages, it must be used together with a mode of operation.
The choice of mode strongly affects the security properties of the resulting scheme. For example, ECB encrypts blocks independently, CTR turns AES into a keystream generator, and GCM provides authenticated encryption.
Same primitive, different security behaviour
AES-ECB, AES-CTR, and AES-GCM all use AES as their underlying block cipher, but they do not provide the same guarantees. The main difference comes from the mode of operation, not from the block cipher itself.