Definition
Password-Based Key Derivation Function 2
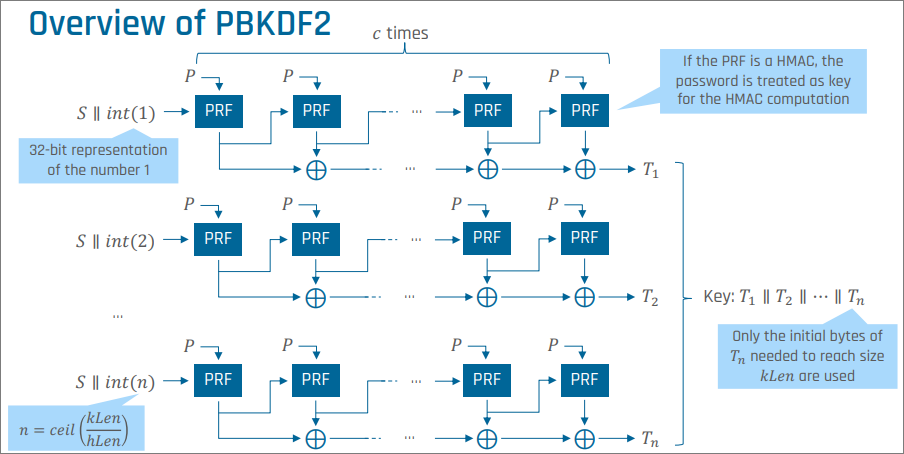
PBKDF2 is a password-based key derivation function defined in PKCS #5 / RFC 2898. It derives a cryptographic key of arbitrary length from a password by iterating a pseudorandom function.
For password-based authentication, the derived key is used as the stored “hash” of the password.
Parameters
Pseudorandom Function
A keyed function with two parameters and fixed output length (for example, HMAC-SHA256).
Password
The user-provided secret.
Salt
A random per-user value.
Iteration Count
The number of iterations; typically to .
Desired Key Length
The number of bytes to output.
Algorithm
For each block :
The derived key is the concatenation truncated to bytes:
Security
Work Factor
An attacker must perform evaluations of the PRF per guess. The iteration count directly scales the attacker’s cost.
Parallelisability
PBKDF2 can be configured to arbitrarily increase computation time. However, it requires little memory and can be easily parallelised. ASICs and GPUs can therefore be used for highly parallelised offline attacks.
Not Memory-Hard
Modern alternatives — scrypt, Argon2, yescrypt — are memory-hard: they derive the key from a large array whose computation is time-intensive. Elements are accessed depending on the password characters. Parallelising an offline attack then requires either huge memory availability (to store the array) or large computation time (to recompute array elements on the fly).
PBKDF2 is not memory-hard. An attacker can evaluate many PRF calls in parallel on GPUs or ASICs. For new systems, memory-hard alternatives are preferred.